Scope/Description
- This article will walk through the process of configuring Ceph RGW to use SSL with HAProxy Loadbalancer.
Prerequisites
- Ceph Cluster running either Nautilus(v14) or Octopus(v15)
- RGW gateways configured and operating
- ceph-ansible-45d version 1.4.2 or greater
- SSL Certificate
Steps
Obtain SSL Certificate
- Run these commands on the ansible master node.
- When generating the Certificate Signing Request (CSR) you will need to answer the questions as they are relevant to your environment. Gathering this info before starting this process is a benefit. More info on what info is required can be found here, Genertating CSR with openssl.
- In the below examples, mydomain is used as a placeholder, you should use your specific domain.
- If you already have a ssl cert (in .crt format) skip to Concatenate KEY AND CRT to create PEM file for haproxy.
- If you already have a ssl cert in .pem format skip to Copy Pem to each RGW.
- Generate a unique private key (KEY)
[root@vosd1 ceph-ansible]# openssl genrsa -out mydomain.key 2048
- Generate a Certificate Signing Request (CSR)
[root@vosd1 ceph-ansible]# openssl req -new -key mydomain.key -out mydomain.csr - At this point there are two options, using a self signed cert, or registering with a third party SSL authentication authority. This doc will continue with the self signed route. If registering with third party, once you recieve your .crt start the process again at step (4)
- Creating a Self-Signed Certificate (CRT)
[root@vosd1 ceph-ansible]# openssl x509 -req -days 365 -in mydomain.csr -signkey mydomain.key -out mydomain.crt
- Concatenate KEY and CRT to create PEM file for haproxy
[root@vosd1 ceph-ansible]# cat mydomain.key mydomain.crt >> mydomain.pem
- Copy PEM to each RGW
[root@vosd1 ceph-ansible]# ssh rgw1 "mkdir -p /etc/ssl/private/" && scp mydomain.pem rgw1:/etc/ssl/private/
Configure Ansible Varibles
- With the pem generated and placed on the rgws, we are going to configure the ansible varibles so we can run the loadbalacer playbook.
- Run these below commands from the ansible master
- Create a [rgwloadbalancers] group in hosts file, and add your rgw gateways to it.
[root@vosd1 ceph-ansible]# cp group_vars/rgwloadbalancers.yml.sample group_vars/rgwloadbalancers.yml
- Open the group_vars/rgwloadbalancers.yml for editing
- Uncomment all varibles, explanation on the ones which should be changed below
haproxy_frontend_port : When not using SSL this is the port the S3 service is accessible from haproxy_frontend_ssl_port: When using SSL this is the port the S3 service is accessible from haproxy_frontend_ssl_certificate: The path to the SSL cert local to the RGW server. This is the path to the .pem file we created above virtual_ips: The IPs haproxy will use as the floating IP(s). Multiple entires supported, recommended not to use more IPs than rgws. virtual_ip_netmask: The netmask for the virtual IPs above virtual_ip_interface: The interface that will host the VIP
Example of Ansible Variables
haproxy_frontend_port: 80 haproxy_frontend_ssl_port: 443 haproxy_frontend_ssl_certificate: /etc/ssl/private/your-pem-here.pem virtual_ips: 192.168.1.1 virtual_ip_netmask: 16 virtual_ip_interface: public-bond
Deploy HAProxy with Ansible
- With the pem generated and placed on the rgws, ansible variables configured, we are now ready to deploy HAProxy.
[root@vosd1 ceph-ansible]# ansible-playbook radosgw-lb.yml
Verification
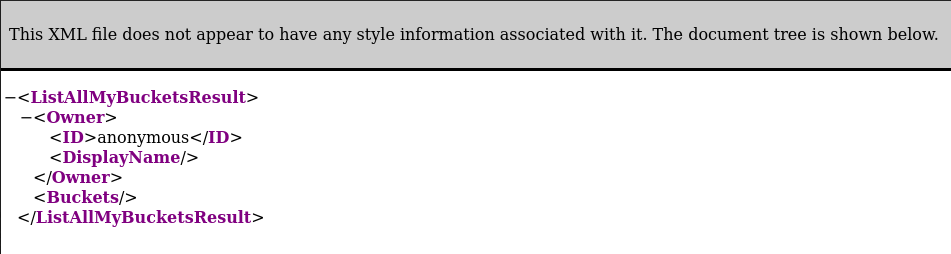
- Point your browser to one of the VIPs at the SSL port specified, if you are met with the following everything is working correctly. Note that if you used the self signed cert you will be met with warning page first.
Troubleshooting
- The .pem format should look like the following, (the keys will obviously be different for each person but the headings and format should look like below)
-----BEGIN RSA PRIVATE KEY----- MIIEpQIBAAKCAQEAuBA1qjPvlrArwNHt9Ny8bD6fS9gkY2AIcN1FbYtCSlUx3UFK /SMWYHUx9K5H6FCYP6YSZe2U2AUZdwNsBRmM9BgXLLbnOMJxEf15k8ZvCgnVUTJh ...... 7nZv0uAZ70hRM4cfORzRcttAJeImOI/MHe14rhWgizZZlIaCA7CF6Imb31l+dq6z YginGvUdoySr2N8q8yZSpOvxYgxBrePsqj37sYYofQamH0bI6uwVVk8= -----END RSA PRIVATE KEY----- -----BEGIN CERTIFICATE----- MIIDMjCCAhoCCQCfx9aLU4aT3jANBgkqhkiG9w0BAQsFADBbMQswCQYDVQQGEwJD QTEUMBIGA1UECAwLTm92YSBTY290aWExDzANBgNVBAcMBlN5ZG5leTERMA8GA1UE ..... Hq17g3a7QOcTYggf9SZgcmfut5Liuz9MxfihEkWOw9hBVudsZqxGyhK/nzSrb4Xz MKCdzzJg0ojbrm4FMbh+SLJzkHmcQiQrMOJLOLNn/eFM/SKXW3PCVseLoUp84FGk LOBZ3974 -----END CERTIFICATE-----
Views: 3698